Compromise of a server with unconstrained deleg allows extraction of TGTs of any user/system that connects. It could be combined with the printer bug to allow forest compromise.
Back in server 2000 first introduced Active Directory, Microsoft had to find a way to allow Servers authenticate to other resources in the context of a user.
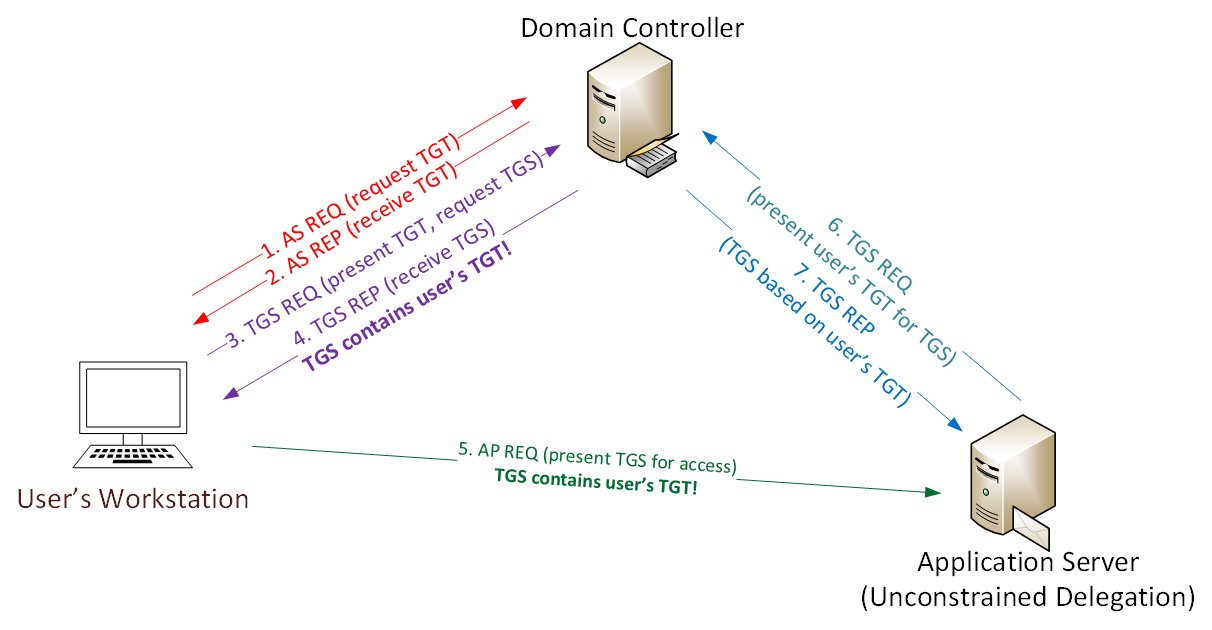
The implemented it by user authenticates to a service on a server via service ticket (TGS). The target service extracts the user’s TGT from the TGS to use for other TGS requests.
Unconstrained Delegation is a privilege that can be granted to User Accounts or Computer Accounts in a active directory environment that allows a resources to authenticate to another resource on BEHALF of a user.
Example:
The user Stuart Authenticates to Workday (Web app) which authenticate to the Payroll server on behalf of stuart to fetch information.
Step by step:
By compromising the 'Workday' server which is set with unconstrained delegation, we can monitor incoming TGS tickets and extract the TGT and use it in further attacks.
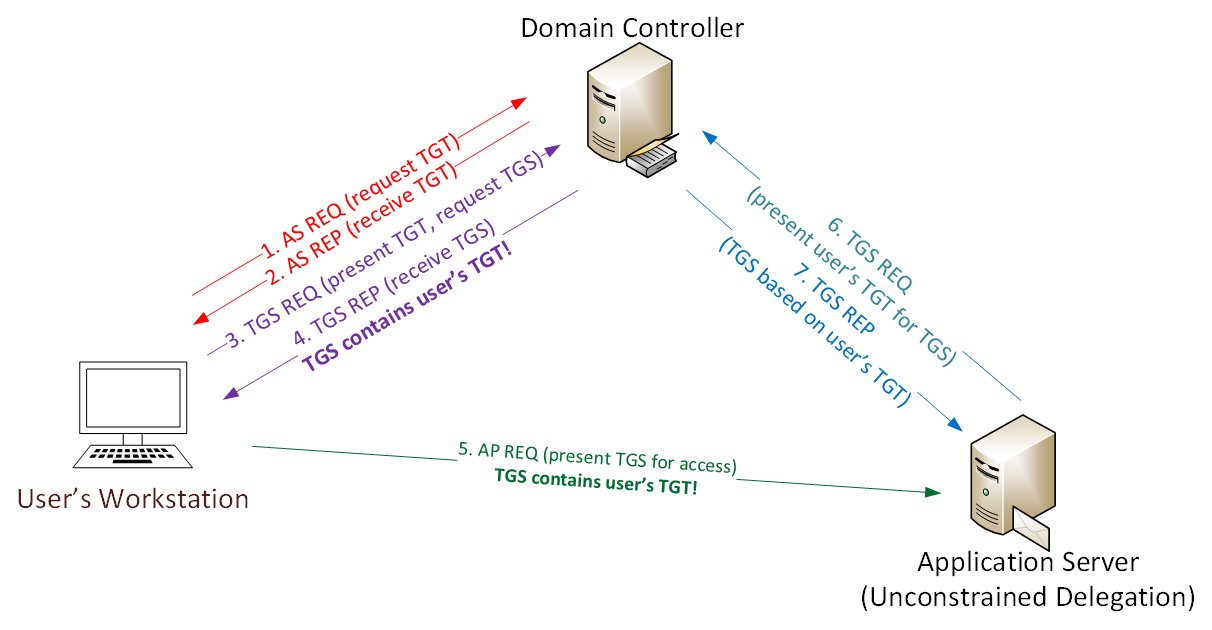
Visio-KerberosUnconstrainedDelegation-visio
The TGS ticket the hosts sends to the server are stored in the server memory, and they could be extracted.
This attack combined with the printer bug is very dangerous for domains, and highly beneficial for attackers..